Hacker Leaks 144GB of Royal Mail Group Data, Blames Supplier Spectos
[ad_1]
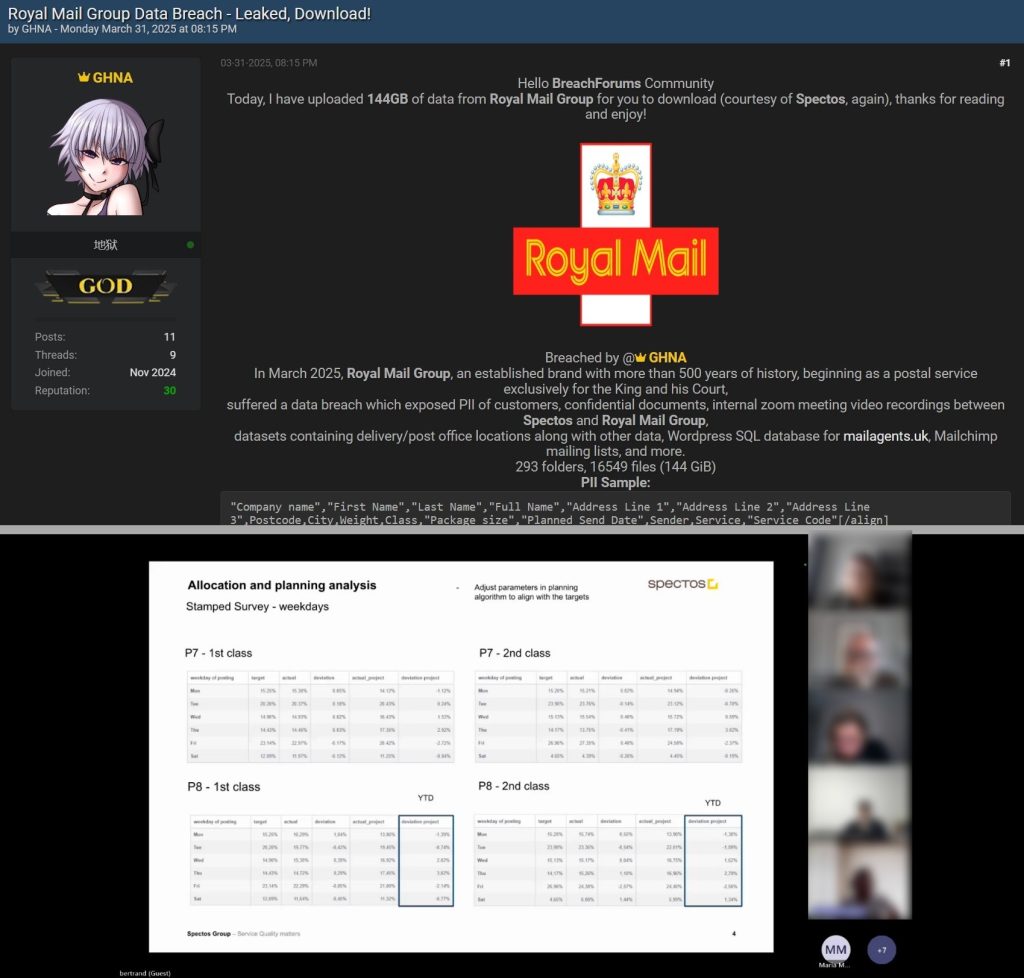
Royal Mail Group, the UK’s centuries-old postal institution, has allegedly suffered a massive data breach resulting in the leak of 144GB of internal files, customer information, and marketing data. The breach was first made public on the cybercrime forum Breach Forum by a user known as GHNA.
144GB of Leaked Data
As seen by the Hackread.com research team, GHNA published a post on Monday, March 31, 2025, stating: “Today, I have uploaded 144GB of data from Royal Mail Group for you to download (courtesy of Spectos, again). Thanks for reading, and enjoy!”
The post included a screenshot of what appears to be a Zoom meeting recording between Royal Mail Group and Spectos, a German-based data analytics and performance management firm.
Spectos has previously been mentioned in association with other leaks, raising questions about whether the vector for this attack was a direct compromise of Royal Mail’s infrastructure or a third-party breach involving vendors with deep system access.
The alleged breach gave the hacker access to a wide range of sensitive data. The leaked archive contains 293 folders and 16,549 files, totaling 144GB. The exposed records include:
- Customer Personally Identifiable Information (PII): Names, full addresses, postal codes, and shipping details, including sender data like business names and services used.
- Internal Communications: Video recordings of meetings, most notably Zoom calls between Spectos and Royal Mail staff.
- Operational Data: Delivery route datasets, post office location information, and backend SQL databases.
- Marketing Infrastructure Data: Mailchimp mailing list exports showing subscriber metadata, campaign tags, and detailed consent information.
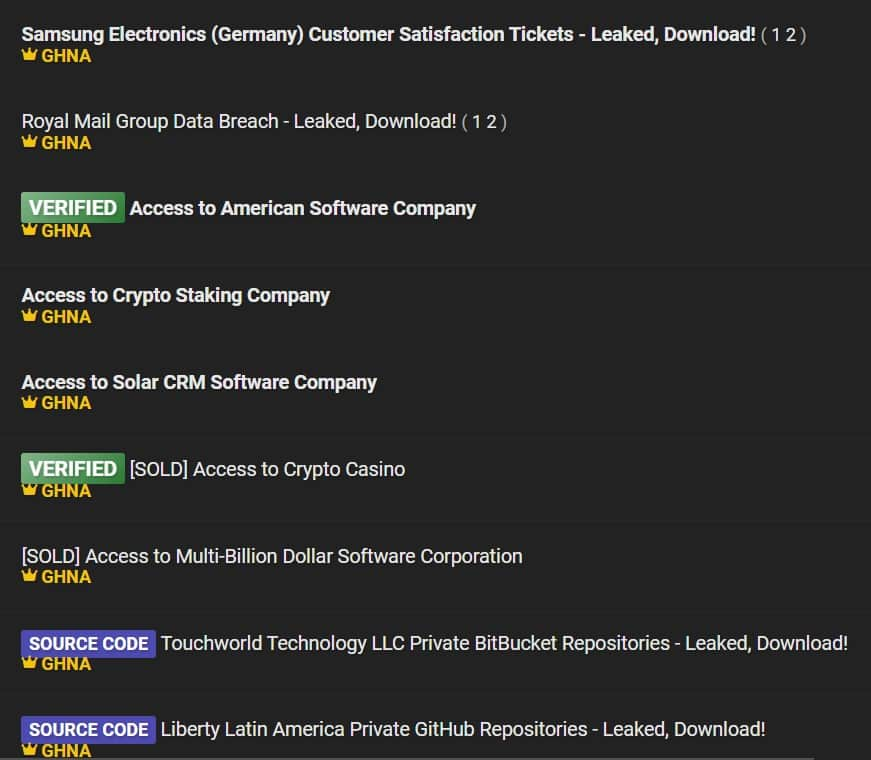
The Hacker: Who Is GHNA?
A closer look at the hacker’s activity reveals that they have been active on Breach Forums since late 2024. GHNA has built a growing reputation by leaking or selling access to several high-profile organizations across multiple industries. Their posts include:
- Multi-billion dollar software firms and solar industry players
- Samsung Electronics (Germany) – Leaked customer satisfaction ticket data
- Touchworld Technology LLC and Liberty Latin America – Source code repositories
- Access to American and European software companies, including CRM and staking platforms
- Crypto-focused targets, such as a staking company and a casino (both verified, with one marked as sold).
Several of these listings have been tagged as “VERIFIED” by the forum’s moderation team, and some have already been sold, indicating that GHNA is not only gaining access to sensitive environments but actively monetizing them.
The Royal Mail Group breach appears to be one of the largest GHNA has published in terms of raw data volume. However, the variety of their previous listings suggests this is part of a broader campaign or ongoing access-as-a-service operation.
Third-Party Connection: Spectos In the Spotlight
Spectos’ name appears multiple times in the breach materials, including in internal documents and recorded video calls. It is unclear whether Spectos was the breach vector or simply involved in the data Royal Mail was managing at the time.
The hacker’s comment, “Courtesy of Spectos, again”, suggests that Spectos may have played a role in how the data was accessed. Given the amount and type of leaked content, it’s possible the compromise happened through a shared system, an integration point, or within Spectos’ own infrastructure.
Royal Mail has acknowledged the situation. In an email to Hackread.com, the company stated, “We are aware of an incident which is alleged to have affected Spectos, a supplier of Royal Mail. We are working with the company to investigate the issue and establish what impact, if any, there may be regarding their data.”
So far, Spectos has not released any public statement about the incident.
Past Breach: Royal Mail’s Security Challenges Continue
This incident is the latest in a series of cybersecurity challenges faced by the Royal Mail Group. In early 2023, the company was targeted by the LockBit ransomware gang, causing major operational disruptions. That attack shut down Royal Mail’s international parcel delivery systems for weeks and forced the organization to issue emergency contingency plans.
That earlier attack was tied to financially motivated ransomware operators. This time, there’s no ransom demand, but the breach might point to a rising interest in Royal Mail’s data, either from opportunistic hackers or those taking advantage of weak links in the company’s vendor network.
Impact and Ongoing Analysis
While the breach hasn’t been confirmed by Royal Mail directly, the company has acknowledged the issue through their vendor, Spectos. If the data is genuine, it could have a wide impact. For customers, it means their details are now out there, which could lead to scams, spam, or even identity theft.
For Royal Mail Group, it puts more pressure on how they handle private data and who they trust to help manage it. And for regulators, it might lead to more questions about whether the company is doing enough to protect people’s information.
At the time of writing, the investigation is ongoing, and no further comment has been made by either Royal Mail or Spectos.
[ad_2]
Source link


